Related Project: View Scenario Creation
Management suspects that some employees may be using TOR browsers to bypass network security controls because recent network logs show unusual encrypted traffic patterns and connections to known TOR entry nodes. Additionally, there have been anonymous reports of employees discussing ways to access restricted sites during work hours. The goal is to detect any TOR usage and analyze related security incidents to mitigate potential risks. If any use of TOR is found, notify management.
DeviceFileEvents for any tor(.exe) or firefox(.exe) file events.DeviceProcessEvents for any signs of installation or usage.DeviceNetworkEvents for any signs of outgoing connections over known TOR ports.DeviceFileEvents TableSearched for any file that had the string "tor" in it and discovered what looks like the user "Stefano" downloaded a TOR installer, did something that resulted in many TOR-related files being copied to the desktop, and the creation of a file called Tor Shopping List.txt in Documents at 2026-02-17T15:11:40.544741Z. These events began at 2026-02-17T14:32:44.0801403Z.
DeviceFileEvents
| where DeviceName == "stefano-tor-bro"
| where FileName contains "tor"
| where Timestamp >= datetime(2026-02-17T14:32:44.0801403Z)
| where InitiatingProcessAccountName == "stefano"
| project Timestamp, DeviceName, ActionType, FolderPath, SHA256, Account = InitiatingProcessAccountName
| order by Timestamp desc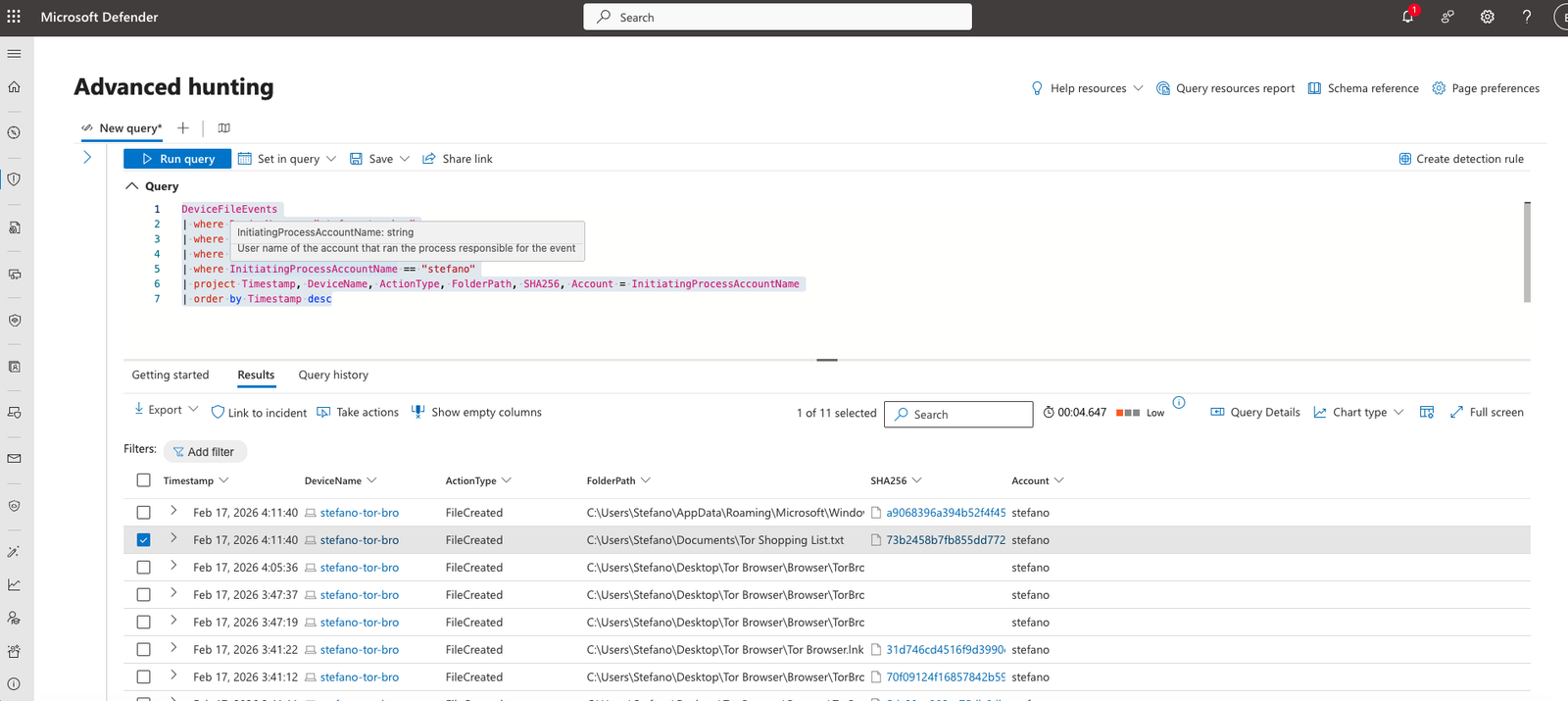
Figure 1: DeviceFileEvents showing TOR file creation
DeviceProcessEvents TableSearched for any ProcessCommandLine that contained the string "tor-browser-windows-x86_64-portable-15.0.6.exe". Based on the logs returned, at 2026-02-17T14:40:53.712063Z, an employee on the "stefano-tor-bro" device ran the file tor-browser-windows-x86_64-portable-15.0.6.exe from their Downloads folder, using a command that triggered a silent installation.
DeviceProcessEvents
| where DeviceName == "stefano-tor-bro"
| where ProcessCommandLine contains "tor-browser-windows-x86_64-portable-15.0.6.exe"
| project Timestamp, DeviceName, AccountName, ActionType, FileName, FolderPath, SHA256, ProcessCommandLine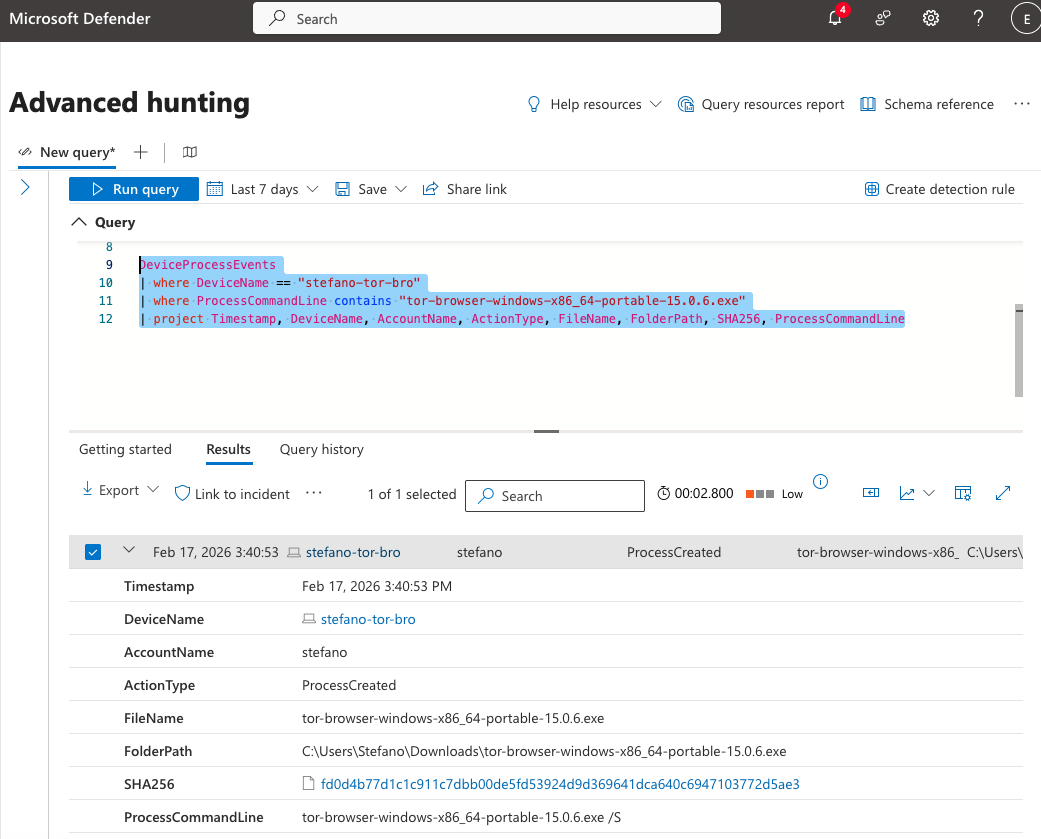
Figure 2: DeviceProcessEvents showing silent installation
DeviceProcessEvents Table for TOR Browser ExecutionSearched for any indication that user "employee" actually opened the TOR browser. There was evidence that they did open it at 2026-02-17T14:46:56.93411Z. There were several other instances of firefox.exe (TOR) as well as tor.exe spawned afterwards.
DeviceProcessEvents
| where DeviceName == "stefano-tor-bro"
| where FileName has_any ("tor.exe", "firefox.exe", "tor-browser.exe")
| project Timestamp, DeviceName, AccountName, ActionType, FileName, FolderPath, SHA256, ProcessCommandLine
| order by Timestamp desc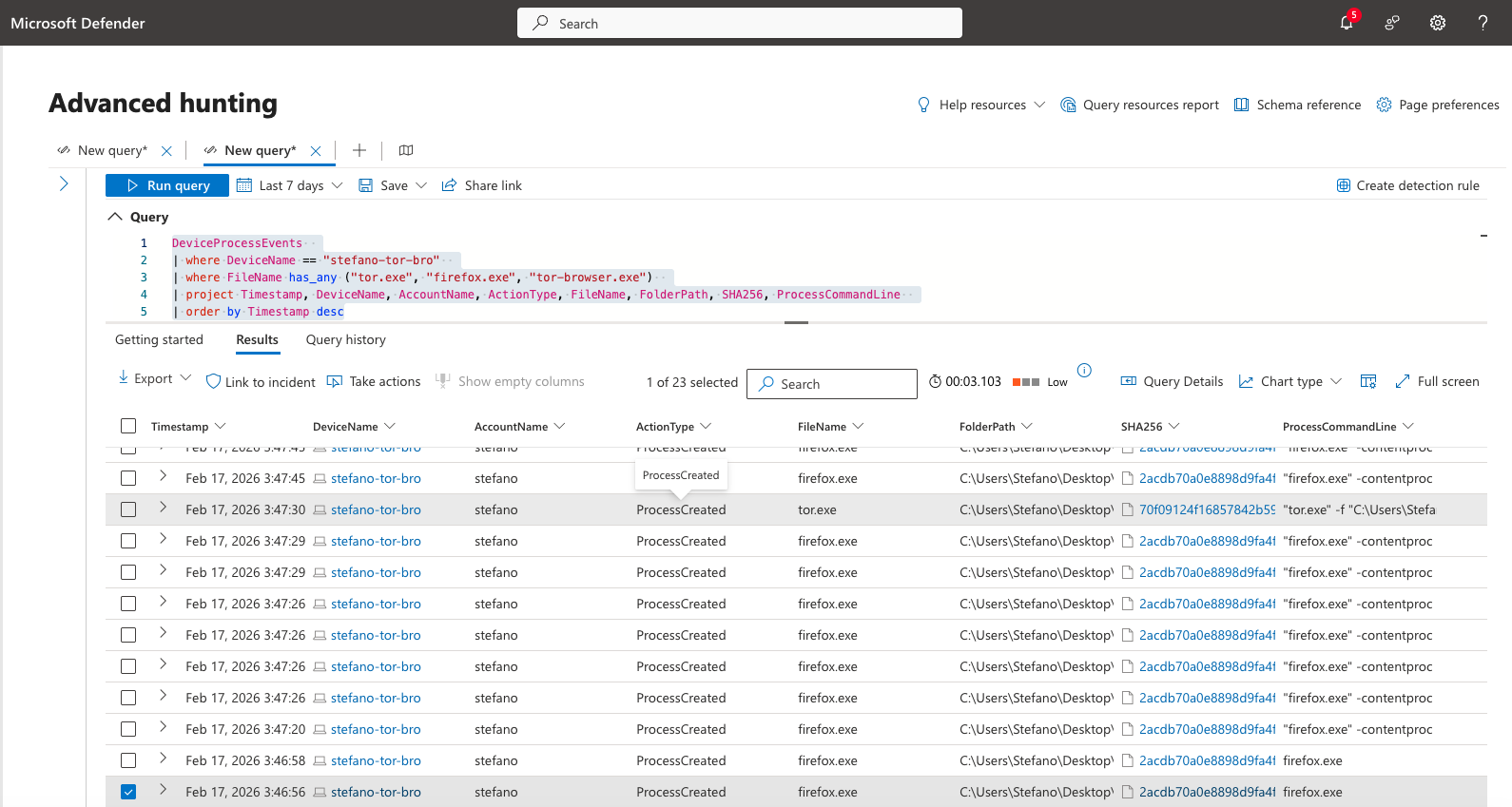
Figure 3: DeviceProcessEvents showing active browser usage
DeviceNetworkEvents Table for TOR Network ConnectionsSearched for any indication the TOR browser was used to establish a connection using any of the known TOR ports. At 2026-02-17T14:48:32.140446Z, an employee on the "stefano-tor-bro" device successfully established a connection to the remote IP address 164.65.1.77 on port 443. The connection was initiated by the process tor.exe, located in the folder c:\users\stefano\desktop\tor browser\browser\torbrowser\tor\tor.exe. There were a couple of other connections to sites over port 9001.
DeviceNetworkEvents
| where DeviceName == "stefano-tor-bro"
| where InitiatingProcessAccountName != "system"
| where InitiatingProcessFileName in ("tor.exe", "firefox.exe")
| where RemotePort in ("9001", "9030", "9040", "9050", "9051", "9150", "80", "443")
| project Timestamp, DeviceName, InitiatingProcessAccountName, ActionType, RemoteIP, RemotePort, RemoteUrl, InitiatingProcessFileName, InitiatingProcessFolderPath
| order by Timestamp desc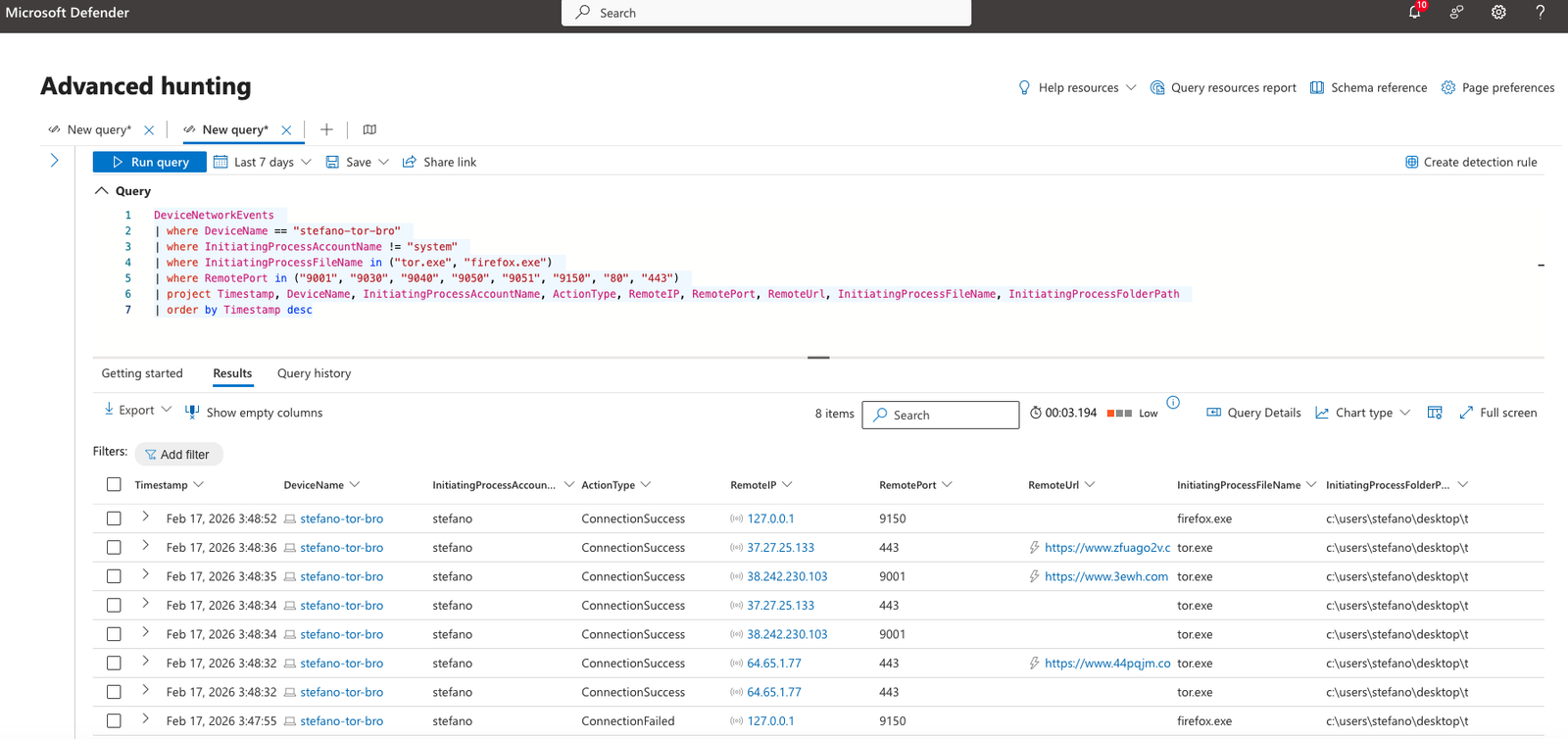
Figure 4: DeviceNetworkEvents showing external connections
2026-02-17T14:32:44.0801403Ztor-browser-windows-x86_64-portable-15.0.6.exe to the Downloads folder.C:\Users\Stefano\Downloads\tor-browser-windows-x86_64-portable-15.0.6.exe2026-02-17T14:40:53.712063Ztor-browser-windows-x86_64-portable-15.0.6.exe in silent mode, initiating a background installation of the TOR Browser.tor-browser-windows-x86_64-portable-15.0.6.exe /SC:\Users\Stefano\Downloads\tor-browser-windows-x86_64-portable-15.0.6.exe2026-02-17T14:46:56.93411Zfirefox.exe and tor.exe, were also created, indicating that the browser launched successfully.C:\Users\Stefano\Desktop\Tor Browser\Browser\firefox.exe2026-02-17T14:48:32.140446Z64.65.1.77 on port 443 by user "stefano" was established using tor.exe, confirming TOR browser network activity.tor.exec:\users\stefano\desktop\tor browser\browser\torbrowser\tor\tor.exe2026-02-17T14:48:34.9307458Z - Connected to 38.242.230.103 on port 9001.2026-02-17T14:48:52.5237094Z - Local connection to 127.0.0.1 on port 9150.2026-02-17T15:11:40.544741ZTor Shopping List.txt on the desktop, potentially indicating a list or notes related to their TOR browser activities.C:\Users\Stefano\Documents\Tor Shopping List.txtThe user "stefano" on the "stefano-tor-bro" device initiated and completed the installation of the TOR browser. They proceeded to launch the browser, establish connections within the TOR network, and created various files related to TOR on their desktop, including a file named Tor Shopping List. This sequence of activities indicates that the user actively installed, configured, and used the TOR browser, likely for anonymous browsing purposes, with possible documentation in the form of the "shopping list" file.
TOR usage was confirmed on the endpoint stefano-tor-bro by the user stefano. The device was isolated, and the user's direct manager was notified.